Definition, utilities and examples of use of log file in computer science
Log file
In computer science, the term log or log file (whose meaning is logbook or simply newspaper) indicates a file on which events are recorded in chronological order and is used to indicate normally:
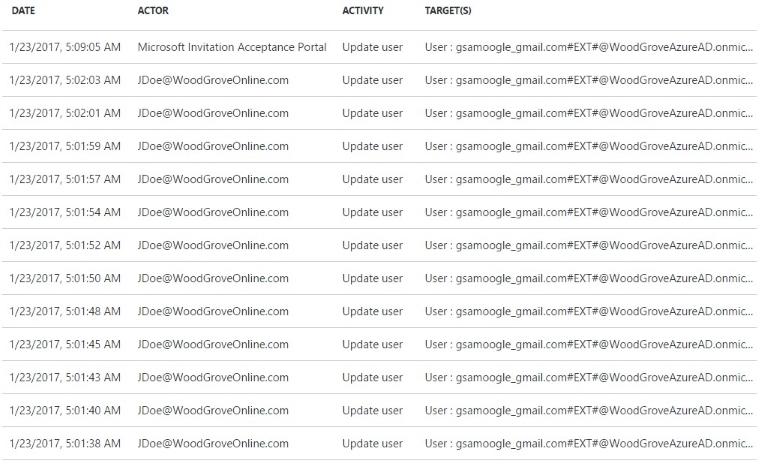
- the chronological recording of the operations as they are performed
- the file or database on which these recordings are stored.
The simplest log, from its origins to the present, is a sequential file always open in writing, which is closed and stored at regular intervals and made available for:
- analysis of error reports,
- production of operating statistics, such as traffic statistics in web services
- restoring previous situations
- analysis of changes made to the database
- analysis of the operations carried out and responsible for these operations
- summary of what happened in a given period of time, for example in chats
The log can also be a data base segment with direct access via timestamp (timestamp) but its use as a chronological record does not change.
To understand how the log files support the management, maintenance and analysis of a complex system, consider how most of the statistical surveys on traffic generated by Internet sites are carried out by programs that analyze and present, in a comprehensible form to the human reader , the data stored moment by moment by the web servers in their log files.
Originally used as a primary source of information for determining server workloads and studying possible improvements in the distribution of those loads, today the data obtained from log files are considered primarily as commercial tools, ie:
- as information on the success of an Internet site,
- as a means to learn about browsing habits and preferences of users connecting to a site,
- as credentials for selling services (such as advertising space).
To provide another example where the logs provide valuable help in the administration of a system, let’s think now of the case in which a network administrator finds a hacker attack on a machine inside the network. Going to consult the log files generated by the system, he will be able to check if any external intrusions have been recorded and which system vulnerabilities have been exploited. It is clear that after this analysis it will be possible to take the right precautions by making technical improvements to the system.
Considering instead a distributed system whose components are executed on different machines connected in a network, the management of the logs is different from the previous cases. In fact, to optimally manage the distributed application we should be able to verify the execution of the various components by going to consult the individual log files generated by these and residing on the different machines. Therefore it would be desirable to collect the log files on a single “repository” machine so as to facilitate consultation and maintain an archive accessible at any time.
Another example in which it is desirable to have a log archive is in the banking sector. Think of the logs produced during the login phase of a user on the website of their bank. Assuming that the website offers the customer the remote view of all the data concerning his current account, it would be useful, both for reasons of confidentiality and to have a history of all the operations carried out, to store the log files produced during the access to the web server on a repository server. The latter, of course, must include all possible precautions for security purposes to prevent access by malicious users.
Considering the aspects of detection and diagnosis of errors, it is important to emphasize that the logs are an indispensable support tool, just think of a process belonging to a distributed application, which through its suspension, could lead to the stalling of the entire application. Then through the analysis of the logs, generated by the operating system, one could go back to which process led to the suspension of the application and then solve the problem.
The above examples are just some of the scenarios in which the log file is a fundamental tool for managing more or less complex systems.
